Why IPFS?
While this course will mainly focus on IPFS, there are a number of proposed solutions to blockchain-based and decentralized storage. The general architecture remains quite similar between them, so it will help to review how these systems operate before comparing them. In this lesson, we’ll explore how IPFS uses blockchain to track and move files through it’s network.
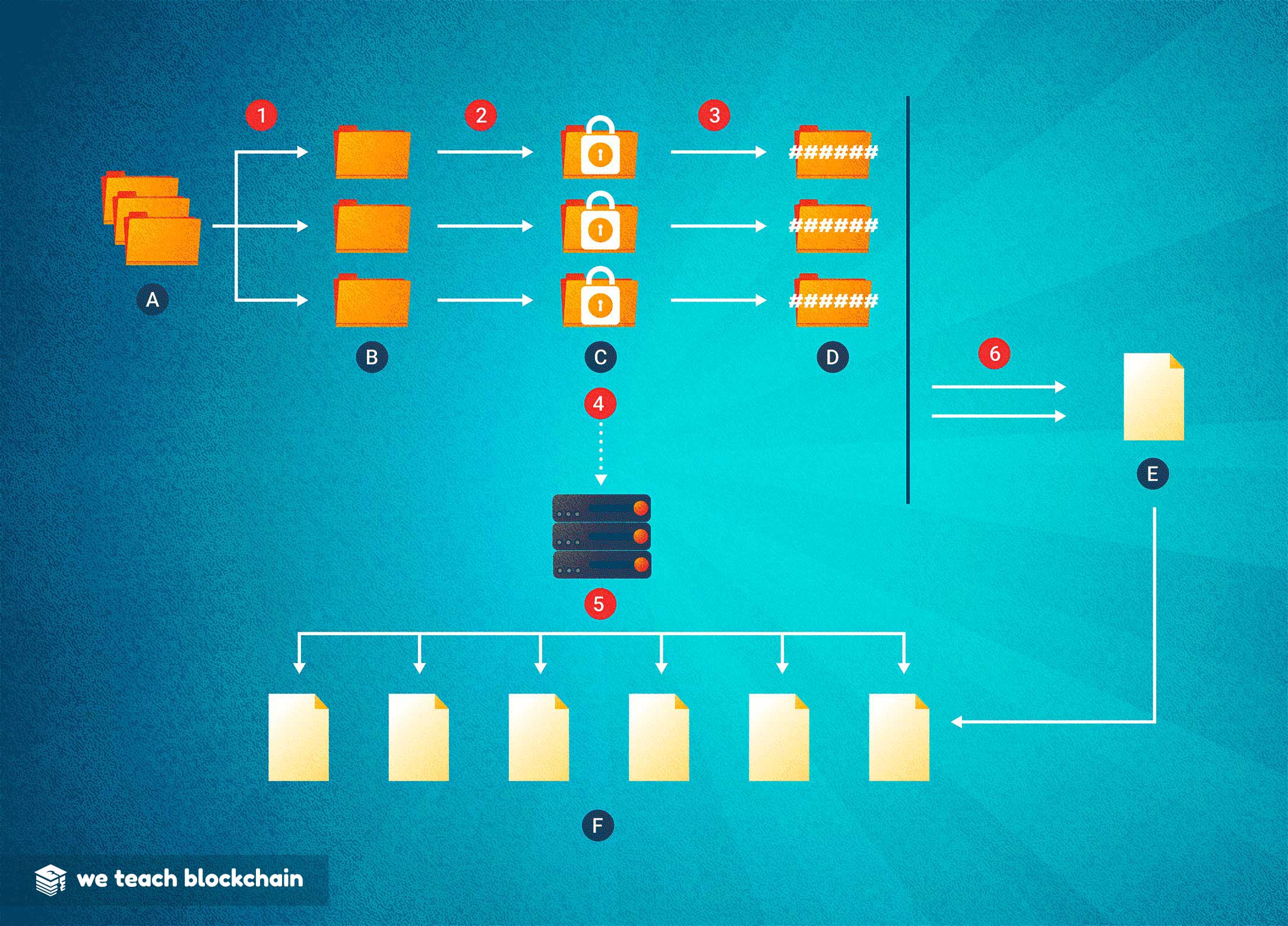
HOW BLOCKCHAIN STORAGE WORKS:
Because blockchains must be stored on all nodes of the network, data on them is expensive. As a result, hashes are used to represent an image of each piece of a file, and the pieces can then be safely distributed to storage nodes without risk of substitution of compromise.- First, the A: Data is broken into B: Shards
- Next, the shards are encrypted (C: Encrypted Shards)
- Then, each encrypted shard is hashed D: Hashes
- The hashes are added to the ledger (E: Blockchain Ledger)
- Each shard is then transmitted through the network (F:) to Distributed Nodes with a Synced Ledger
GENERAL PROCESS
While not all decentralized storage networks are the same, this general process applies to most of the ones in development today.
1. Shard Data
In order to optimize storage and retrieval of files, data is broken down into tiny packets which can each be stored on a different node.
2. Encryption
Each shard is encrypted to anonymize and sterilize the data before public storage.
3. Signatures
In order to uniquely track each shard or file, a hash signature is created that represents each unit of storage uniquely. This will be used to verify that nodes are storing the correct files at the correct addresses.
4. Replication
In a decentralized network, it’s important to have multiple redundant versions of each file. This allows nodes to join and leave the network as they see fit without the file being unavailable.
5. Distribution
Shards are then distributed across the network to a group of nodes to maximize availability.
6. Recording
In a truly decentralized network, a ledger or blockchain can be used to record when and where files are stored, and to ensure that parties are held accountable for breaches of trust.
In the next section, we’ll cover in more detail how IPFS implements this functionality.




