The Bitcoin blockchain was created to allow a decentralized network to coordinate and reach “consensus,” or agreement on the confirmation of shared data. Blockchains were created to solve the problem of how users coordinate data with people, around the world, who they don’t know or trust?
In this lesson and the next, we’ll walk through how the Bitcoin network comes to agreement on transaction data.
But first, lets cover hashing as it is an integral part of the Bitcoin Proof-of-Work consensus mechanism.
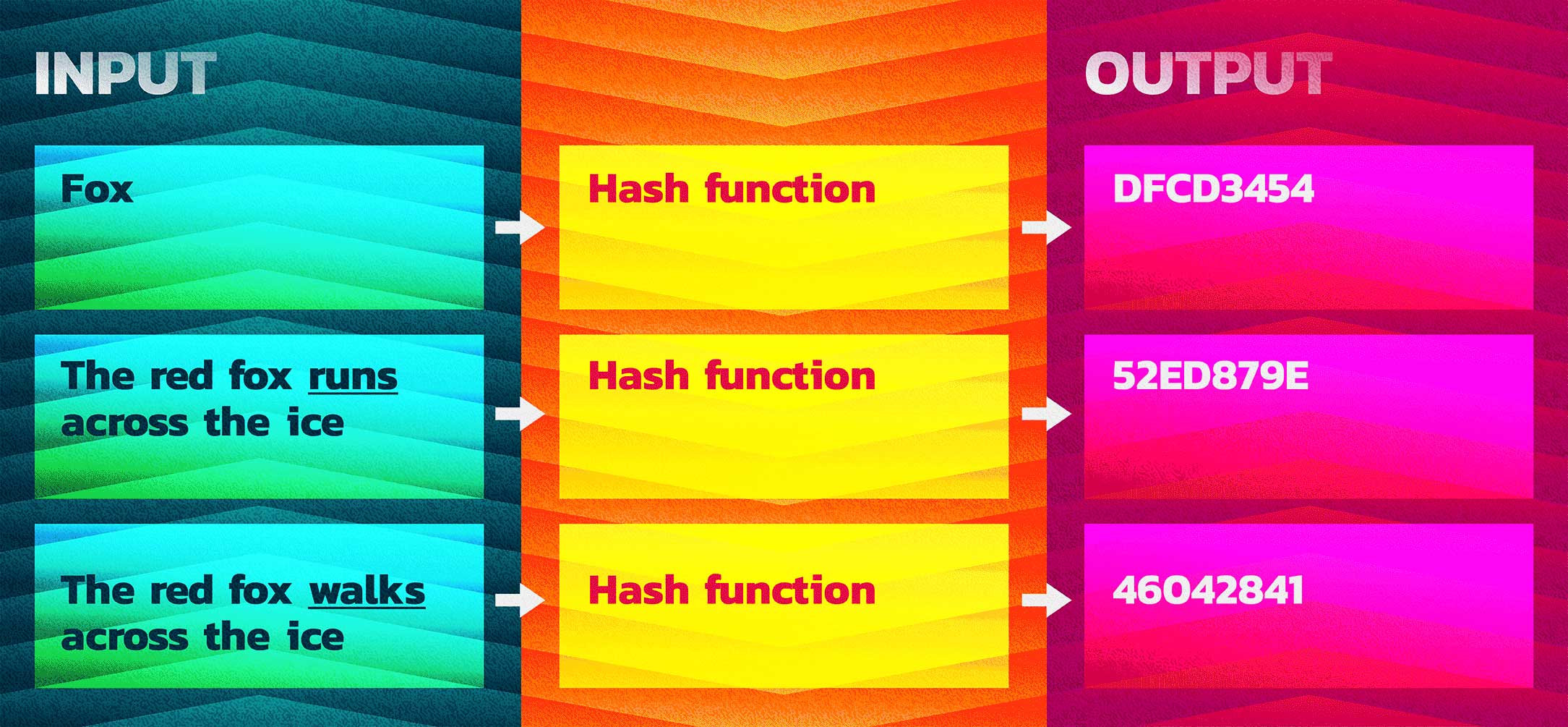
A hash function takes an input value and creates an output value deterministic of the input value. For any input value X, you will always receive the same output value Y whenever the hash function is run. In this way, every input has a determined output.
Properties of hashes:
- Fixed length
- No matter the size of the input, the output will be a uniform size
- Easy to verify, infeasible to reverse
- Any change in the input, no matter how small, will result in a different output
- The output can be called the hash value, digest, or simply a hash
This is very useful in a number of ways. It allows you to use a hash as a nearly unforgeable identifier of data which can then be used to validate that data. The hash of data can also be used in a table to facilitate the quick lookup of that data.
Bitcoin uses hash in many ways. For example, they are used to create transaction ID’s and to summarize and secure the data in a “block” of transaction data via Merkle trees.
MERKLE TREE
A tree constructed by hashing paired data (the leaves), then pairing and hashing the results until a single hash remains, the Merkle root.And now that hashes are out of the way, let’s get back to understanding how the Bitcoin network makes decisions on which data is valid, and which is not.
When trying to visualize this process, it is helpful to keep the picture of nodes (computers) on a distributed network in your head. Remember, Bitcoin is not a business or corporation, there is no CEO, no one entity is in control of it. Bitcoin is simply a network of computers all running the same, or compatible, software.
Let’s walk through the Bitcoin blockchain proof-of-work consensus process with an example:
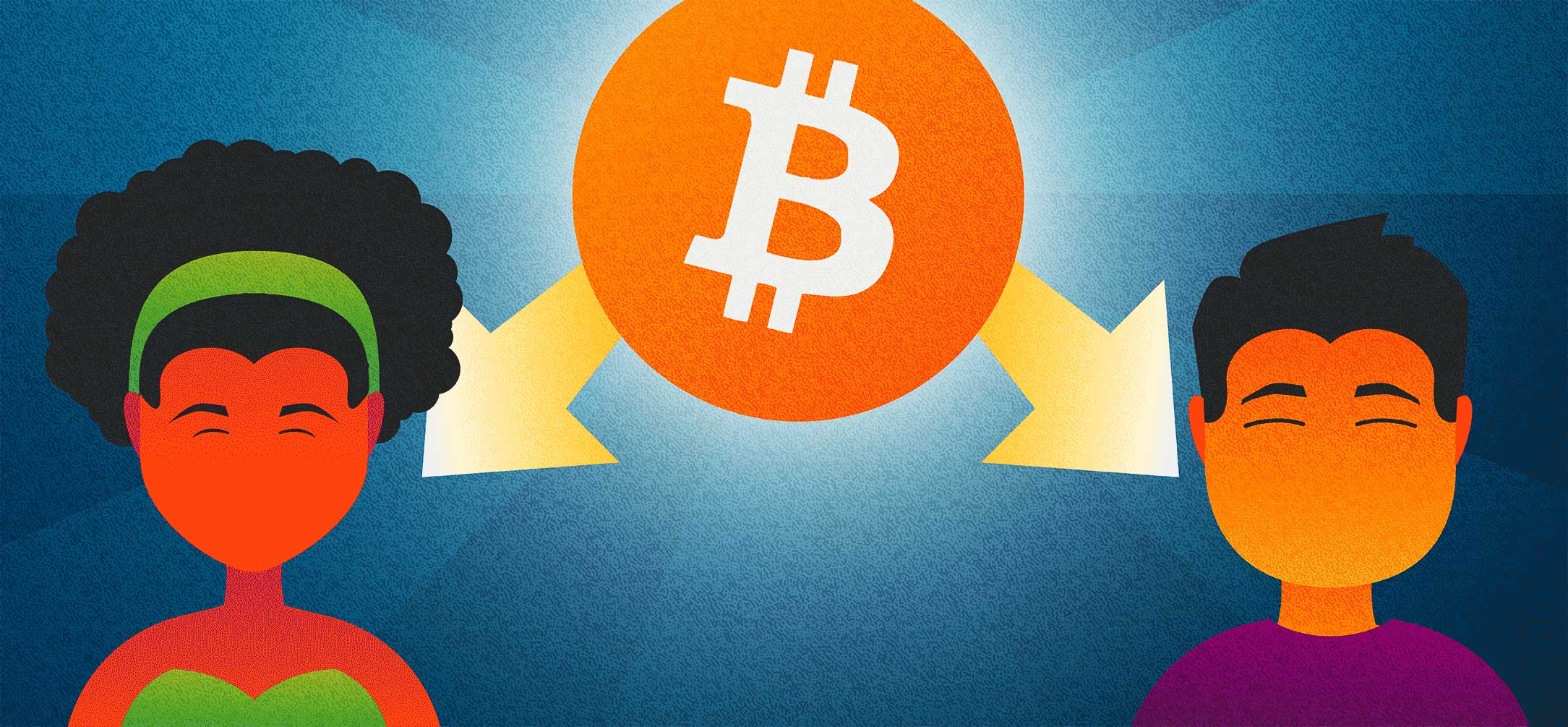
You have one bitcoin that you are trying to double spend. You create a perfectly valid bitcoin transaction sending your 1 BTC (the abbreviation for the currency unit of Bitcoin) to Alice. You sign that transaction and broadcast it to the Bitcoin peer-to-peer (P2P) network. However, at the same time, you create an also perfectly valid transaction sending that 1 BTC to Bob, sign and broadcast it. How will the network decide which transaction is valid and which transaction is to be rejected as a double spend?
Every node on the Bitcoin network contributes to “consensus,” the process by which the data is agreed upon and becomes the ‘truth’ on the network. However, certain nodes, called miners, play a very important role in this process.
The Bitcoin software creates a competition between mining nodes who do the work of gathering transaction data into “blocks.” In this competition, the winning miner receives a reward for their work and their block of data becomes a part of the blockchain.
The mining reward plays a very important role in providing economic incentives to do the work of maintaining the network. Miners, who are simply people running computers with a lot of processing power, are competing with each other to create a valid block of Bitcoin transaction data that will be accepted by the network. When a miner’s block of data is accepted by the network, they are given some bitcoin as a “mining reward” or “block reward”. This happens in a special transaction called a coinbase transaction (not to be confused with Coinbase the company).
When the Bitcoin network was launched in 2009, the reward was 50 BTC per block. This reward halves (called halving) every 4 years (or 210,000 mined blocks) until it reaches an amount too small to transfer on the Bitcoin network. The current block reward is 6.25 bitcoin, as it has halved three times from the original 50 BTC reward. The last Bitcoin was originally scheduled for the year 2140, but due to variations in difficulty adjustments, will likely occur before then.
To create a valid block and win the competition, a miner needs to validate all the transactions in the block and then find a hash for the block that meets with the current network requirements.
The Bitcoin software is designed to self adjust it’s settings so that a block is found roughly every ten minutes. This is done via a network difficulty setting. Roughly every two weeks, or every 2016 blocks, all the nodes on the network calculate how quickly valid blocks were “found” or “mined” on the network. If valid blocks of transaction data were mined more frequently than every 10 min, the difficulty requirement will go up. If blocks were minded less often than every 10 min, the difficulty requirement will do down.
The difficulty requirement is simply the format of the hash of the block data.
When the difficulty requirement goes up, then the network will only accept hashes that start with a greater number of zeros. Effectively, an extra digit is added to the variable being sought, making it more difficult to solve and create a block. Difficulty adjustment is changed to keep block production as close to ten minutes as possible.
For example, the first hash below might not be ‘difficult’ enough to meet current network standards, while the second hash might be satisfactory.
A low-difficulty hash
A higher difficulty hash
This involves some luck as a miner will not be able to determine what the hash will look like prior to running the data through the hashing function. However, we call it difficulty rather than luckiness as the more computing power miners put into the process(relative to the rest of the network) the more likely they are to be lucky enough to find an acceptable hash.
A miner attempts to find an acceptable hash simply by hashing the block data together with a random number called a “nonce.”
NONCE
An arbitrary number that can be used just once in cryptographic communication. In the case of bitcoin mining, a nonce is added to the block data to produce variation in hashing output.A miner will hash the block data, again and again, each time trying a different nonce until they are successful in finding a valid block hash, or until another miner has done so.
Because of the way hash functions work, finding a compatible hash is a matter of trial and error that can take a considerable amount of computing power. Yet, verifying that a hash is valid is very quick and easy.
This hashing is intentional busy work called “proof-of-work,” a concept first developed as a method to combat spam emails in 1993.
This competition plays out with a miner winning the competition and receiving a reward roughly every 10min.
In the next lesson, we’ll see how this competition determines which transaction in a double spend is valid and which is rejected. But first, here are some mining-related terms to get familiar with:




